What is Digital Forensics?
Regardless of how you entered the field of digital forensics, it is common to feel a little lost in the beginning. So, if you’re brand new to this field or would like a refresher on understanding digital forensics, this blog is for you.
What is digital forensics?
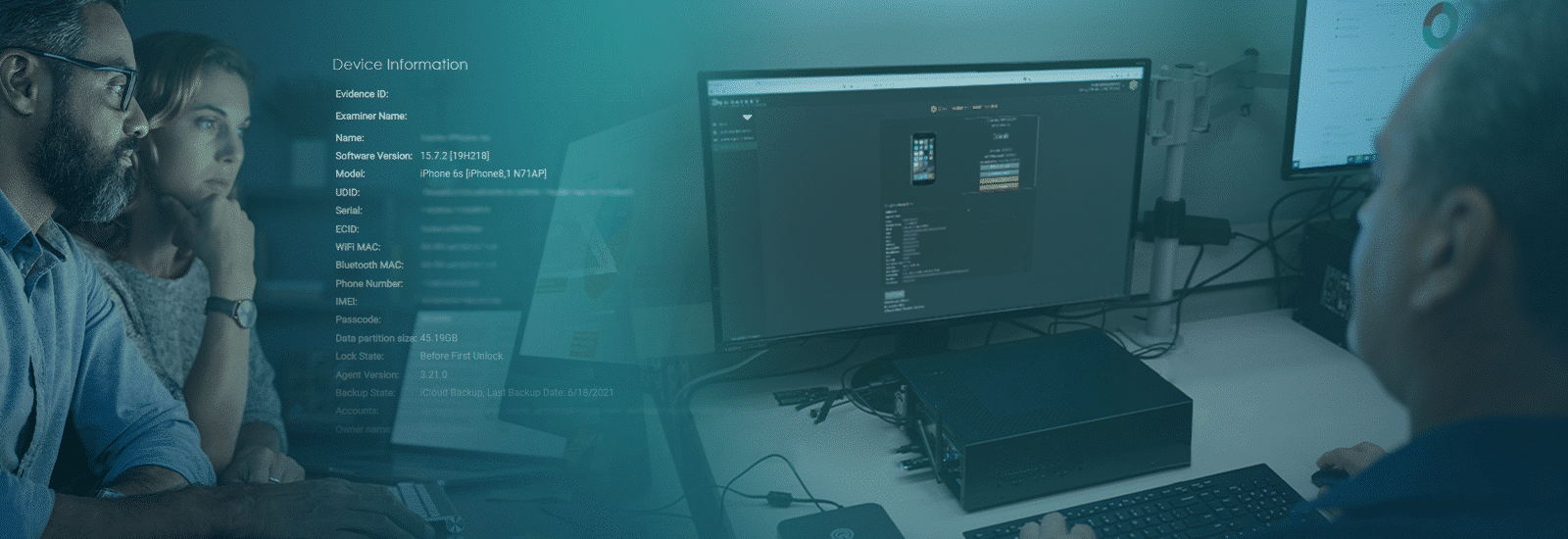
Simply put, digital forensics uses special tools and techniques to collect, analyze, and report on digital evidence. Once the evidence is collected, you can use it in a court of law to help prove or disprove a particular theory or piece of information. There are many different focus areas within digital forensics, but some of the most common include:
Computer forensics: This area of digital forensics deals with identifying, preserving, and extracting evidence from computers. Investigators in this field must be familiar with a wide range of computer hardware and software.
Vehicle infotainment systems: In recent years, vehicle infotainment systems have become more and more complex, with many of them including internet-connected features. As a result, these systems can be a goldmine of evidence for investigators.
Mobile devices: Mobile devices are another common focus area for digital forensics investigators. These devices can contain a wealth of evidence, which we highlight in other blog posts and the Investigator’s Corner. (Login credentials are required for access.)
Smart devices: With the rise of the Internet of Things, digital forensics investigators may be called upon to examine smart devices such as TVs, thermostats, and even refrigerators.
Computer systems: Of course, traditional computer systems are still a significant focus for digital forensics investigators. These systems can contain a wealth of evidence.
In the early days, digital forensics was labeled as computer forensics since most of the technology involved in those early investigations was only computers. Over time, the discipline naturally expanded to include all devices capable of storing digital data and has since been re-branded to digital forensics. Devices that store digital data can consist of anything from your personal computer to your refrigerator. In today’s world, devices that store digital data are part of our everyday lives, and one of the most notable device types almost everyone has is the mobile phone.
What is mobile device digital forensics and why is it important?
Mobile device digital forensics is a subcategory of digital forensics, and it is the process of recovering data from mobile devices. This data can be used to track down a suspect, understand a crime, or gain insights into a person’s life.
Here are a few reasons why mobile device digital forensics is essential to investigations today:
- Mobile devices contain a wealth of evidence that can be used in any type of investigation.
- In many cases, they are often the only source of evidence.
- Mobile device digital forensics can be used to track down a suspect who may be hiding their tracks on a traditional computer system.
- Mobile device digital forensics can help investigators understand how a crime was committed and who was responsible.
What tools and techniques do you need for mobile device digital forensics?
To properly conduct mobile device digital forensics, you need a few essential tools and techniques.
Tools
- Computer System : Run digital forensics imaging and analysis software to process digital evidence
- Network Isolation Hardware : Isolate devices from radio frequency signals to maintain evidence integrity
- Portable Batteries and Device Cables : Ensure on-scene officers have the equipment and accessories they need to properly secure seized devices
- GrayKey : Access and extract encrypted or inaccessible data from mobile devices.
- Data Analysis Software : Import extracted mobile device data into analysis software to begin examining digital evidence
- Device Storage : Safely store mobile device extractions and simplify chain of custody and data integrity
- External Data/Evidence Storage : Relieve storage space from computer systems and store evidence long term
Techniques
- Preserve Digital Evidence: Dedicated evidence intake personnel should be educated on the proper way to preserve digital evidence. Properly seizing and storing digital evidence can be paramount to your investigations due to the security implemented on digital devices. Educating team members on proper device handling is worthwhile, even if that is the only time they will interact with the evidence.
- Copy, Copy, Copy: Once the evidence is back at your lab, you must create a forensic image, or copy, of the digital evidence. You will conduct your investigation on the forensic image as opposed to the evidence item itself. While manually searching the device itself is sometimes necessary, this is not typical in most investigations.
- Nerd Out with Hashes: After you create your forensic image, a hash value will be reported for the newly created file. This hash value results from a calculation or hash algorithm performed on the forensic image obtained from the device. This hash value is important as it is used to verify the integrity of your forensic image throughout the life cycle of your investigation.
- Ask the Investigator: It can be beneficial to ask the investigator many questions about the case before beginning your analysis. Anyone in this position has heard the line “Give me everything.” As you can imagine, that can be an overwhelming amount of data, and without applying techniques to filter through the data, evidence could be missed.
- Maintain Chain of Custody: Whatever methods are applied to search for data, examinations of the evidence must be thorough and proper note-taking is critical. The results from any examination need to be repeatable, and logging who has interacted with the evidence at any point during the investigation helps prove evidence authenticity and document chain of custody in court.
Digital forensics, specifically mobile device digital forensics, is at the forefront of investigations. And the devices that are seized are changing and advancing daily. As a Digital Forensic Investigator (DFI), it is important to keep up with the latest and greatest tools and stay up to date with training. Staying abreast of current trends in the field is beneficial to your investigative techniques and can lead to more productive acquisitions and analysis of digital evidence items.
To learn more about mobile device digital forensic tools like Magnet GRAYKEY, and get the most out of your digital investigations with Magnet AXIOM, please get in touch with us.